Book a Tuesday, in-person meeting this tax season with James Rogers by clicking here. Tax season meetings available from 11 am - 1 pm weekly on Tuesdays begining February 25th and ending on April 1st.
Book a Tuesday, in-person meeting this tax season with James Rogers by clicking here. Tax season meetings available from 11 am - 1 pm weekly on Tuesdays begining February 25th and ending on April 1st.
Last updated by CISO December 9, 2024
Written Information Security Plan (“WISP”)
Rogers CPA Firm, LLC (“Firm”/”we”/”our”/”us”) recognizes the importance of protecting client information and is committed to creating effective administrative, technical, and physical safeguards to protect client information from unauthorized access. We are a certified public accounting firm that provides accounting, tax, and consulting services to businesses, fiduciaries, and individuals. In the normal course of business, we receive clients’ sensitive information, which may include social security numbers, tax identification numbers, bank account information, investment/brokerage statement numbers, and other confidential information.
In compliance with applicable federal and state laws, Rogers CPA Firm, LLC has developed this Written Information Security Plan (“WISP”), which sets forth the Firm’s policy and procedures for evaluating and addressing the electronic and physical methods of accessing, collecting, storing, using, transmitting, and protecting Personal Identifiable Information (“PII”).
Firm Governance and Compliance
James D. Rogers, the Firm owner, will serve as the Chief Information Security Officer (“CISO”) and is designated as the person who shall be responsible for overseeing and updating the WISP as needed. Should we appoint another CISO in the future, they will report directly to the Firm owner. The CISO may assign or delegate other Firm representatives to oversee and coordinate elements of the WISP. Any questions regarding the implementation of the Plan or interpreting this document should be directed to the CISO or his or her designees.
The CISO will verify compliance with this policy through various methods, including but not limited to periodic walkthroughs, monitoring, testing, business tool reports, and internal and external audits. The CISO will report all findings, regulatory and state security law changes, and any other information technology security–related matters directly to the Firm owner.
Compliance with this policy is mandatory for all employees and independent contractors. Employees should notify their immediate supervisor or the CISO upon learning of suspected violations of this policy and the supervisor and/or CISO is responsible for notifying the Firm owner. Employees who violate this policy (including knowingly not notifying their supervisor or CISO of such suspicions) will be subject to education on security measures and possibly disciplinary action, up to and including termination of employment.
Safeguards for the Protection of Client Personal Identifiable Information
Our Firm has made reasonable efforts to identify potential internal and external risks to the security, confidentiality, and integrity of client information that could result in the unauthorized disclosure, misuse, alteration, destruction, or other compromises of PII.
We have implemented the following safeguards for controlling risks associated with accessing, collecting, storing, using, transmitting, and protecting PII, including the handling and/or disposing of PII, whether in electronic, paper, or other form. The first six items (the “Security Six”) were developed by the Internal Revenue Service as part of their “Taxes-Security-Together” Checklist:
“Security Six” Safeguards
1. Anti-virus software and anti-malware software.
All system security software, including anti-virus, anti-malware, and internet security, shall be up to date and installed on any computer and mobile device that stores or processes PII. We will rely on external information technology advisors to recommend all software in this regard and will request from them an external audit triennially to ensure proper implementation and future recommendations. Full system scans will be conducted weekly.
2. Firewalls for hardware and software.
We use physical and software firewalls to protect all connected hardware and software. We will rely on external information technology advisors to recommend or approve all physical software firewalls. We will request an external audit triennially to ensure proper implementation and future recommendations.
3. Multi-factor authentication.
The Firm requires all personnel and contractors to use multi-factor authentication to access any application that holds PII. The Firm requires any device with access to means of authentication to be encrypted.
4. Back-up software/services
PII obtained by the Firm will be stored in the cloud using only third-party storage vendors that either 1) have been certified to have, at a minimum, either un-expired ISO 27001 certificates, or have had Systems and Organizations Controls (SOC) Report 2, type 2 audits with opinions of effective controls within the prior year, or 2) outsource storage to another third-party service who has made the audit of their SOC Report 3 (whitepapers) available to the public and the audits result in opinions of effective controls. The CISO or assisting personnel will obtain such certifying reports from vendors on an annual basis. (Note: Non-disclosure agreements restrict us from making SOC 2, type 2 reports available to clients.)
The CISO will be responsible for ensuring that all PII stored in the cloud will be backed up to an external hard drive once a week. Any external drives used by the Firm must have encryption enabled and a password must be set to access the device, and the password must meet the requirements listed in bullet point 8 below. The CISO will be responsible for ensuring that external drives containing PII are stored in a locked filing cabinet on-site.
Access to PII from the cloud will be downloaded by Firm personnel as needed. The CISO is responsible for instructing personnel to delete weekly all downloaded files containing PII from computers and mobile devices. Files in recycling bins should also be deleted.
5. Encryption
The CISO will be responsible for ensuring that all computers and mobile devices are encrypted and can only be opened with a password. The Firm does not employ a server.
6. Virtual Private Networks (“VPN”)
The Firm is committed to the use of VPNs on computers and mobile devices at all times when used outside of its private network. It will only rely on VPNs that use AES 256-bit encryption or a higher standard. CISO is responsible for installing VPNs on all computers and mobile devices.
Additional Safeguards
7. Private Network Security
The Firm will not allow the use of its private network to persons who are not firm personnel or information technology consultants. A separate network shall be available onsite for non-personnel. CISO is responsible for changing the password to its private network once every three months.
8. Passwords
- All computer users at the Firm will have their own accounts and passwords.
- The Firm requires passwords to be unique to each user and to be unique to each application. Passwords are to be at least 10 characters (including capital and lower-case letters, numbers, and symbols), and randomly generated by a password-keeper application approved by the CISO. This application will be used to log in to any application holding PII.
- Personnel will be prompted and required to update their passwords monthly.
- The Firm prohibits the sharing of accounts and/or passwords with others.
- The Firm specifically prohibits personnel from using passwords previously used within the prior year.
- The CISO will perform regular walkthroughs of workstations to ensure no passwords are written down or in visible sight.
9. Additional Security Measures Regarding Email, Web, and Downloaded Files
The CISO is responsible for maintaining additional threat intelligence software to safeguard from phishing, impersonation, spoofing, spam, and malware. The firm’s policy is that the following settings in such software are always enabled:
- Settings that ensure multifactor authentication is used for all email accounts.
- Settings that ensure that all users have mailbox intelligence enabled and automatically send suspicious messages to quarantine.
- Settings that monitor for viruses, malware, and other malicious content in message attachments and quarantine detected messages.
- Settings that allow intelligence to identify all users’ email patterns with frequent contacts and spot phishing attempts.
- Settings that ensure that messages from any domain that holds PII are subject to impersonation protection checks by intelligence and quarantine suspect messages. CISO will add to the list of protected domains as new domains are utilized and will review the list of protected domains annually.
- Settings that ensure that intelligence will monitor for impersonation of firm personnel via email and that automatically quarantine suspect messages.
- Settings that block all firm personnel from accessing apps that do not support modern authentication.
- Settings that quarantine messages detected to have malware or phishing regardless of the message being opened.
- Settings that automatically detect and quarantine uncommon file types.
- Settings that allow intelligence to automatically quarantine messages that it detects with “high confidence” of being spam.
- Settings that allow intelligence to automatically quarantine messages that it flags as phishing attempts.
- Settings turning on an audit log for user and admin activity and retain the log for 90 days.
- Settings that detect inbound messages that have a “bulk complaint level” and move those emails to junk.
- Settings that disallow automatic message forwarding.
- Settings that subject the number of outbound messages from each user to hourly and daily limits and block users that reach those limits.
10. Inventory of Hardware
An inventory of Firm hardware is maintained and updated as needed that lists all hardware (PCs, mobile devices, hard drives, USB drives, phones, routers, printers, scanners, copiers, fax machines, and other devices commonly used by Firm personnel) used by the Firm that may store PII. The inventory list will identify as appropriate the location, principal user, and any other information deemed necessary by the Firm as a reasonable safeguard to protect client information and comply with this policy.
11. Physical Security
It is our policy to maintain physicle for employing a security service in this regard. Any physical location is required to have cameras, motion detectors, entry sensors, glass break sensors, smoke detectors, and flood sensors to ensure adequate protection of PII when personnel are unavailable. The service should offer immediate notification to the firm owner and the proper response authorities should a breach occur.
PII found on physical documentation will be stored in locked filing cabinets onsite in client hanging files until such files can be scanned for cloud storage. CISO will review the filing cabinets annually to ensure physical files are stored no longer than one year. All discarded physical files are to be shredded by a micro-cut shredder or incinerated.
12.Cyber Insurance Coverage
The Firm maintains insurance coverage for first-party and/or third-party cyber matters. Questions regarding insurance coverage, cyber resources, and/or the requirements for reporting matters to the insurance carrier(s) should be directed to the CISO.
13. Admin Rights
The Firm will only assign software admin rights to the CISO or the firm owner. All other personnel will have limited user accounts.
14. Related Firm Policies
The Firm maintains the following additional policies and procedures that support the Firm’s commitment to creating effective protocols for protecting client information:
- Record Retention and Destruction Policy
(last updated on December 6, 2024, by the CISO) which sets forth the Firm’s protocols and procedures for the protection and physical security of all hard-copy files, electronic files, computer hardware, software, data, and documentation from misuse, theft, unauthorized access, and environmental hazards.
- Security Breach Procedures and Notifications Policy
(last updated on December 6, 2024, by the CISO) which sets forth the Firm’s protocols and procedures in the event of discovering a breach of security.
- Data Breach Incident Contact List
(Last updated on December 6, 2024) which provides contact information for those who should be contacted first in the event of a breach.
- Firm Hardware Inventory List (Last updated on December 6, 2024)
Note: Should the Firm hire an employee or contractor, that person will be required to sign a confidentiality agreement and an acknowledgment of understanding the WISP and its objectives. This section will be updated to list those agreements at that time.
FTC’s Safeguard Rules Checklist
In addition to the safeguards noted above, the CISO is also responsible for monitoring and updating the Firm’s Safeguards Rule Checklist, which is incorporated by reference in this Plan in the Addendum. The Safeguards Rule Checklist tool was disseminated by the FTC, promulgated by the IRS in Publication 4557, Safeguarding Taxpayer Data (Rev. 7-2021), and adopted for use by the Firm. The tool is designed to help track the Firm’s compliance efforts with three additional key areas of risk that are important as they relate to information security in relevant areas of our operations: Employee Management and Training; Information Systems; and Detecting and Managing System Failures.
Employee Management and Training
All Firm Owners, Managers, Supervisors, and Seniors are tasked with supporting the CISO to ensure that all personnel are aware of and comply with this Plan and other applicable policies and procedures. This includes but is not limited to, developing and applying appropriate performance standards, training curriculum, and control practices and procedures designed to provide reasonable assurance that all employees understand and support the Firm’s commitment to safeguarding client information. Refer to the Firm’s responses to specific compliance efforts noted on the Firm’s Safeguards Rule Checklist.
Information Systems
The CISO works closely with the Firm’s technology team, including external information technology professionals, to assess and mitigate through applicable policies and procedures the risks associated with the Firm’s information systems, including network and software design; information processing; and storage, transmission, and disposal of client information. Refer to the Firm’s responses to specific compliance efforts noted on the Firm’s Safeguards Rule Checklist.
Detecting and Managing System Failures
The Firm takes reasonable steps to deter, detect, and defend against security breaches as noted on the Safeguards Rule Checklist. In addition, the Firm has a Security Breach Procedures and Notifications Policy that addresses protocols in the event of a suspected breach to ensure timely and appropriate responsiveness.
Future Updates
In consideration of our Firm’s size and complexity, the nature and scope of the professional services we render to our clients, and the sensitivity of the information we collect, the Firm has determined that compliance with this Plan meets known current regulatory and legal requirements.
The CISO will periodically review the effectiveness of the program with the Firm owner and will reassess the risk factors as well as any material changes to the Firm’s operations and recommend changes to the Plan as necessary. Subsequent updates to the Plan will be communicated to all employees under Firm protocols.
Addendum: Safeguards Rule Checklist
[Source: Excerpt from “Checklist for Creating a Plan” contained in IRS Publication 4557 (Rev. 7-2021):
https://www.irs.gov/pub/irs-pdf/p4557.pdf
].
The Safeguards Rule requires companies to assess and address the risks to customer information in all areas of their operation, including three areas that are particularly important to information security: Employee Management and Training; Information Systems; and Detecting and Managing System Failures.
Not each of these recommendations will apply to circumstances found in tax preparer offices, but they still provide a good guide for the creation of a security plan and reinforce IRS recommendations that tax professionals establish strong security protocols. Depending on the nature of their business operations, Firms should consider implementing the following practices:
| Employee Management and Training Information systems include network and software design, and information processing, storage, transmission, retrieval, and disposal. Following are some FTC suggestions on maintaining security throughout the life cycle of customer information, from data entry to data disposal. |
|||
| Ongoing |
Done |
N/A |
|
|
|
|
|
The success of your information security plan depends largely on the employees who implement it. Consider these steps: |
| ☐ |
☒ |
☐ |
Control access to sensitive information by requiring employees to use “strong” passwords that must be changed on a regular basis. (Tough-to-crack passwords require the use of at least ten characters; upper- and lowercase letters; and a combination of letters, numbers, and symbols.) |
| Ongoing |
Done |
N/A |
|
| ☐ |
☒ |
☐ |
Use password-activated screen savers to lock personnel computers after a period of inactivity. |
| ☐ |
☒ |
☐ |
Develop policies for appropriate use and protection of laptops, PDAs, cell phones, or other mobile devices. For example, make sure personnel store these devices in a secure place when not in use. Also, consider that customer information in encrypted files will be better protected in case of theft of such a device. |
|
|
|
|
Train personnel to take basic steps to maintain the security, confidentiality, and integrity of customer information, including: |
| ☐ |
☒ |
☐ |
• Locking rooms and file cabinets where records are kept; |
| ☐ |
☒ |
☐ |
• Not sharing or openly posting passwords in work areas; |
| ☐ |
☒ |
☐ |
• Encrypting sensitive customer information when it is transmitted electronically via public networks; |
| ☐ |
☒ |
☐ |
• Refer calls or other requests for customer information to designated individuals who have been trained in how your company safeguards personal data. |
| ☐ |
☒ |
☐ |
• Reporting suspicious attempts to obtain customer information to designated personnel. |
| Information Systems Information systems include network and software design, and information processing, storage, transmission, retrieval, and disposal. Here are some FTC suggestions on maintaining security throughout the life cycle of customer information, from data entry to data disposal. |
|||
| Ongoing |
Done |
N/A |
|
|
|
|
|
Know where sensitive customer information is stored and store it securely. Make sure only authorized personnel have access. For example: |
| ☐ |
☒ |
☐ |
Ensure that storage areas are protected against destruction or damage from physical hazards, like fire or floods. |
| ☐ |
☒ |
☐ |
Store records in a room or cabinet that is locked when unattended. |
| ☐ |
☒ |
☐ |
When customer information is stored on a server or other computer, ensure that the computer is accessible only with a “strong” password and is kept in a physically secure area. ( IRS suggestion: If using a cloud storage service, use a strong password and multi-factor authentication options, and beware of thieves posing as providers.)
Where possible, avoid storing sensitive customer data on a computer with an internet connection.
CISO Note: Client information is stored on the cloud with vendors who have passed security audits. An external hard drive backing up data is updated weekly and stored securely. Physical files are to be scanned and shredded after no longer than one year. |
| ☐ |
☒ |
☐ |
Maintain secure backup records and keep archived data secure by storing it offline and in a physically secure area. |
| ☐ |
☒ |
☐ |
Maintain a careful inventory of your company’s computers and any other equipment on which customer information may be stored. |
|
|
|
|
Take steps to ensure the secure transmission of customer information. For example: |
| ☐ |
☒ |
☐ |
When you transmit credit card information or other sensitive financial data, use a Secure Sockets Layer (SSL) or other secure connection, so that the information is protected in transit. ( IRS suggestion: Transport Layer Security 1.3 is newer and more secure.) |
| ☐ |
☒ |
☐ |
If you collect information online directly from customers, make secure transmission automatic. Caution customers against transmitting sensitive data, like account numbers, via email or in response to an unsolicited email or pop-up message. |
| Ongoing |
Done |
N/A |
|
|
|
|
|
Dispose of customer information in a secure way and, where applicable, consistent with the FTC’s Disposal Rule . For example: |
| ☐ |
☒ |
☐ |
Burn, pulverize, or shred papers containing customer information so that the information cannot be read or reconstructed. |
| ☐ |
☐ |
☒ |
Destroy or erase data when disposing of computers, disks, CDs, magnetic tapes, hard drives, laptops, PDAs, cell phones, or other electronic media or hardware containing customer information.
CISO Note: Nothing disposed of. |
| Detecting and Managing System Failures Effective security management requires your company to deter, detect, and defend against security breaches. That means taking reasonable steps to prevent attacks, quickly diagnosing a security incident, and having a plan in place for responding effectively. Consider implementing the following procedures: |
|||
| Ongoing |
Done |
N/A |
|
| ☐ |
☒ |
☐ |
Monitor the websites of your software vendors and read relevant industry publications for news about emerging threats and available defenses. |
|
|
|
|
Maintain up-to-date and appropriate programs and controls to prevent unauthorized access to customer information. Be sure to: |
| ☐ |
☒ |
☐ |
• Check with software vendors regularly to get and install patches that resolve software vulnerabilities; |
| ☐ |
☒ |
☐ |
• Use anti-virus and anti-spyware software that updates automatically; |
| ☐ |
☒ |
☐ |
• Maintain up-to-date firewalls, particularly if you use a broadband internet connection or allow employees to connect to your network from home or other off-site locations; |
| ☐ |
☒ |
☐ |
• Regularly ensure that ports not used for your business are closed |
| Ongoing |
Done |
N/A |
|
|
|
|
|
Use appropriate oversight or audit procedures to detect the improper disclosure or theft of customer information. It is wise to: |
| ☐ |
☒ |
☐ |
• Keep logs of activity on your network and monitor them for signs of unauthorized access to customer information; |
| ☐ |
☒ |
☐ |
• Use an up-to-date intrusion detection system to alert you of attacks; |
| ☐ |
☒ |
☐ |
• Monitor both in- and out-bound transfers of information for indications of a compromise, such as unexpectedly large amounts of data being transmitted from your system to an unknown user; and |
| ☐ |
☒ |
☐ |
• Insert a dummy account into each of your customer lists and monitor the account to detect any unauthorized contacts or charges. |
|
|
|
|
Take steps to preserve the security, confidentiality, and integrity of customer information in the event of a breach. If a breach occurs: |
| ☐ |
☐ |
☒ |
• Take immediate action to secure any information that has or may have been compromised. For example, if a computer connected to the internet is compromised, disconnect the computer from the internet;
CISO Note: No signs of a breach were observed. |
| ☐ |
☐ |
☒ |
• Preserve and review files or programs that may reveal how the breach occurred; and
|
| ☐ |
☐ |
☒ |
• If feasible and appropriate, bring in security professionals to help assess the breach as soon as possible.
|
|
|
|
|
Consider notifying consumers, law enforcement, and/or businesses in the event of a security breach. For example: |
| ☐ |
☐ |
☒ |
• Notify consumers if their personal information is subject to a breach that poses a significant risk of identity theft or related harm; |
| ☐ |
☐ |
☒ |
• Notify law enforcement if the breach may involve criminal activity or there is evidence that the breach has resulted in identity theft or related harm; |
| ☐ |
☐ |
☒ |
• Notify the credit bureaus and other businesses that may be affected by the breach. See Information Compromise and the Risk of Identity Theft: Guidance for Your Business ; and |
| ☐ |
☐ |
☒ |
• Check to see if breach notification is required under applicable state laws. |
| ☐ |
☐ |
☒ |
• ( IRS suggestions : Practitioners who experience a data loss should contact the IRS and the states. Also, consider having a technical support contract in place, so that hardware events can be fixed within a reasonable time and with minimal disruption to business availability.) |
[1] As noted in IRS Publication 4557 (Rev. 7-2021) , the IRS is currently recommending that passwords be a minimum of eight characters, the NIST standard, and for administrators, a minimum of 16 characters.
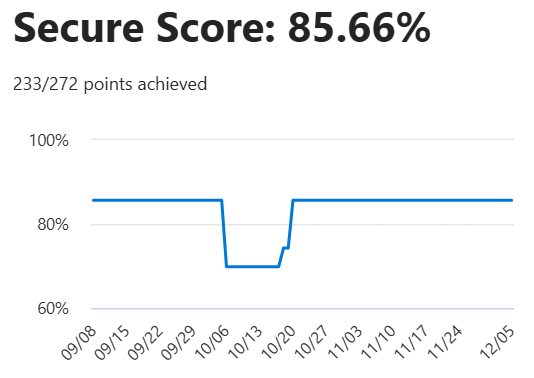
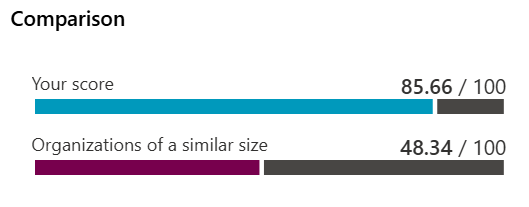
Microsoft Defender Security Score & Benchmarking - December 6, 2024
CONTACT INFORMATION
James D. Rogers, CPA
(803) 348-4150
james.rogers@rogerscpafirm.com
PO Box 84097
Lexington, SC 29073

Copyright Rogers CPA Firm, LLC 2021
